**Update: 5/13/2022 – updated the log file path and an additional section for validating Work From Home scenario**
Now that Microsoft Teams supports Dynamic Emergency Calling, how can you troubleshoot or validate your configuration? This post will cover the steps to help if your configuration is not populating the proper address when emergency dialing or testing via 933.
I will not be covering the configuration of Dynamic Emergency calling with Teams; if you need a refresher, I suggest taking a look at the Technical Training Video and the accompanying PPT deck.
The next few steps will show you how to create the diagnostic logs in a Teams Desktop app and analyze it for Dynamic Address validation for troubleshooting.
- First, you need to completely Exit Teams client and reopen it, then navigate to the Calling Icon on the left rail to trigger the client to detect the network.

2. Get the client logs from a Teams client by going to the taskbar to right-click the Teams icon and select “Collect Support Files”. Diagnostic log files will be generated at the following location :
- Windows file location:
%userprofile%\Downloads\MSTeams Diagnostics Log <timestamp>\web\MSTeams Diagnostics Log <timestamp>.txt
3. Open the MsTeams Diagnostics Log <timestamp>_calling.txt file in a text editor program like Notepad, Visual Studio, or Notepad++
4. To check to see what the Teams client is reporting as the client’s public NAT’d IP address, do a search for ipaddr

5. Now do a search for EndPointNetwork to see if client’s public IP address is trusted or not. If it returns as Unknown, then there is no match for the Trusted IP of the Teams client and you need to review the configuration in the Teams Admin Portal.
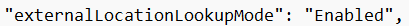
E911 – Work From Home is a recent updated feature for Teams and there is a quick way to validate that the endpoint has the proper setting/policy enabled. Simply search for “externalLocationLookupMode” in the same txt file as previously mentioned. You will be able to quickly see if it is enabled or not. If it shows as “Disabled” then you should double check the Emergency Calling Policy settings and user assignment .
(Screenshot below of it enabled)